What Cybersecurity Framework Do We Recommend for SMEs?
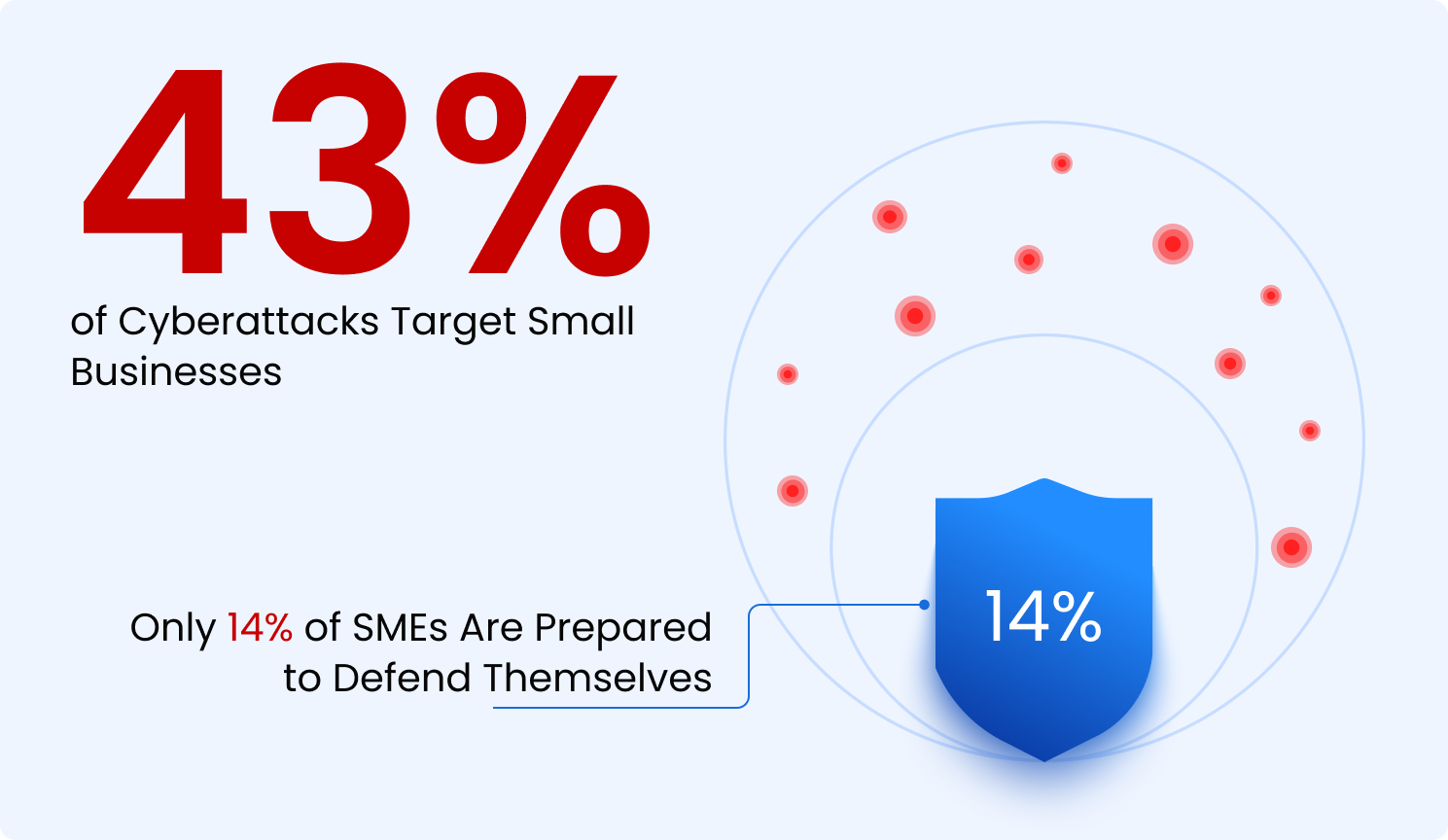
You are an SME (Small-to-Midsized Enterprise) that understands the importance of cybersecurity. You are not surprised that 43% of SMEs are subjected to a cybersecurity attack in a year1.
- Mar 25, 2026

You are an SME (Small-to-Midsized Enterprise) that understands the importance of cybersecurity. You are not surprised that 43% of SMEs are subjected to a cybersecurity attack in a year1. Depending on the nature of your business, you understand that a cybersecurity incident can pose an existential threat. If you are in verticals exposed to heightened cyber risk and regulatory requirements, such as fintech and health tech, your appreciation for the need for robust cybersecurity is particularly acute. However, you are not clear about how to go about achieving it.
Security standards, frameworks and guidelines such as NIST CSF, ISO 27001 and SOC 2, are all aimed at achieving cybersecurity maturity. However, SMEs with limited cybersecurity resources charting their own course based on these can be overwhelming. This blog will help you navigate these and recommend a course of action.
Why SMEs Need Security Frameworks
Structure and Prioritization
Many SMEs think cybersecurity frameworks are for large enterprises with big budgets. In reality, frameworks are even more valuable for smaller organizations, providing structure and direction. Without them, security efforts become reactive, buying random tools and patching issues as they appear. Frameworks act as a roadmap for building security in the right order.
Satisfying Customers and Regulators Through Recognized Benchmarks
SMEs often need to demonstrate cybersecurity maturity to their customers. Conformance with frameworks and standards such as SOC 2, ISO 27001, PCI DSS, and HIPAA make it easier to show customers and partners that security practices follow recognized benchmarks.
Common Frameworks
Following are the main cybersecurity frameworks that apply broadly across all kinds of IT environments independent of verticals:
- NIST Cybersecurity Framework (CSF): Widely used high level risk management framework, with NIST SP 80053 as the detailed control catalog you typically use to implement CSF outcomes. For US federal systems, 80053 control baselines (Low/Moderate/High) are mandatory; in commercial environments, CSF is often voluntary.
- ISO 27001: The leading global standard for managing information security through a risk-based Information Security Management System. The 2022 version defines 93 controls across organizational, people, physical, and technological domains, aligning modern security practices with a certifiable framework. Because companies can be independently audited and certified, ISO 27001 is a powerful signal to customers and regulators that security is managed in a structured, auditable way.
- SOC 2: SOC 2 is an independent audit that evaluates whether a service provider is appropriately protecting customer data using the AICPA’s Trust Services Criteria (security, and optionally availability, confidentiality, processing integrity, and privacy). A SOC 2 Type 2 report is what most buyers look for, because it tests how well those controls actually operate over a period of time. For buyers, a recent SOC 2 Type 2 report is a practical way to reduce due diligence friction, compare vendors to a common standard, and gain assurance that the provider’s security, compliance, and reliability practices are real and consistently followed.
In addition, there are numerous compliance regimes for various verticals and market segments such as PCI DSS, HIPAA/HITRUST, and CMMC.
Meet Mandatory Compliances First
SMEs subject to mandatory compliance requirements such as HIPAA, PCI DSS, and CMMC must focus on their respective mandated compliance first. They should typically allow 6 months to a year before they plan to begin their sales or before they start processing the data subject to the compliance regulations. While compliance should be the initial goal, it should not be the end-goal for SMEs operating on the SaaS model. Modern threats facing SaaS companies are not fully addressed by the level of security achieved by compliance alone.
When Going to Market Obtain a Certification That Helps You Sell
For the US market, particularly SaaS companies, SOC 2 attestation helps meet the benchmark that most enterprise buyers would expect from their suppliers. Outside the US, ISO 27001 is more in vogue. Choose based on your target market. Again, for SaaS companies neither certification should be the end-goal but an important milestone on the way to achieving a level of security that corresponds to the threats they face.
Reasonable, Recognized Security Without a Certification
Several laws and regulations, e.g. HIPAA, GDPR, and CCPA, do not require a certification or a specific set of prescribed controls but ask for “reasonable” or “appropriate” security measures. For budget-constrained organizations that find the certification route costlier and more onerous than they have the budget for, achieving security levels that are recognized by their buyers and target markets and regulators is still possible. While deriving reasonable security from NIST CSF and NIST 800-53 can be a good way to go, for SMEs we recommend going with CIS (Center of Internet Security) Critical Controls. These offer a simpler, prescriptive, and direct way to achieve reasonable security that is widely recognized.
CIS Critical Controls and Community Defense Model
For an SME that needs to know “what exactly should we implement first to defend against the attacks we are most likely to face?”, none of the frameworks and compliance regimes discussed above, on their own, provide a short, empirically prioritized list of concrete safeguards. That is the gap CIS Controls, and the Community Defense Model aim to fill. They are a curated, prioritized list of specific safeguards derived from real-world attack data and broad practitioner input, rather than an exhaustive catalog.
They stand out for SMEs because they are:
- Concise and specific: fewer, clearer controls focusing on things defenders know make a difference, such asset inventory, secure configurations, vulnerability management, access control, monitoring, and backups.
- Prioritized: foundational safeguards come first, so you address the highest impact issues before chasing advanced capabilities.
- Widely recognized: many MSPs, security vendors, and advisory firms now recommend CIS as a practical starting point for small and midsized organizations.
If you only know “we should base our core controls on CIS,” you are already better off than trying to interpret a thousand-line control catalog or build ISO 27001 from a blank page.
What really differentiates CIS, though, is the evidence-based model sitting behind the Controls.
The CIS Community Defense Model: Evidence Behind the Controls
The CIS Community Defense Model (CDM) is a publicly available, evidence-based analysis that connects three layers: real-world attack patterns, MITRE ATT&CK techniques, and specific CIS Safeguards.
In simplified terms, CDM:
- Uses sources like the Verizon Data Breach Investigations Report and MSISAC incident data to identify the most important attack types affecting organizations, such as ransomware, malware, web application attacks, insider misuse, and targeted intrusions.
- Maps those attack types to detailed MITRE ATT&CK techniques, capturing how adversaries actually gain access, move laterally, and achieve their objectives.
- Maps each ATT&CK technique back to specific CIS Safeguards, showing which controls mitigate which attacker behaviors.
The result is a model that can answer a crucial question for SMEs: “If we implement this set of CIS Controls, which real-world attacks are we actually defending against?”
CDM’s analysis shows that the CIS Controls collectively mitigate a very large share of ATT&CK techniques and fully address the techniques observed across the top attack patterns it studies. That is a rare, transparent evidence chain from “controls” back to “the ways attackers actually operate.”
Why You May Not Have Heard of CDM
If CIS Controls are fairly well-known, CDM is still under the radar for many. There are a few reasons for this:
- Audience and messaging: CIS markets the Controls broadly; CDM is presented more as a supporting analysis for practitioners comfortable with ATT&CK and incident data. It sits a layer deeper than most SME-focused content.
- Complexity of the source documents: the full CDM papers are detailed and technical. For a typical SME, the headline (“these controls mitigate the top attack patterns”) is useful, but the underlying mappings can feel like overkill.
- Ecosystem inertia: many organizations, vendors, and auditors are already anchored on NIST or ISO language. Even when CIS + CDM offers a cleaner evidence story, it takes time for mental models and templates to catch up.
That underuse is an opportunity. SMEs that adopt CIS Controls and understand the basics of CDM can tell a stronger story to customers, insurers, and boards: not only do they follow a recognized control set, they can point to a public model showing how those controls map to real-world threats.
CIS + CDM offers something distinctive: a widely recognized, concise set of controls plus an open, documented model that shows how those controls defend against prevalent attacks.
For SMEs looking for concise, prioritized, and evidence-backed security guidance, basing your core control set on the CIS Critical Security Controls and using the Community Defense Model to explain and prioritize those controls is, in our view, one of the strongest options available today.
CIS IG1: The Best Way to Start Wherever You Want to End Up
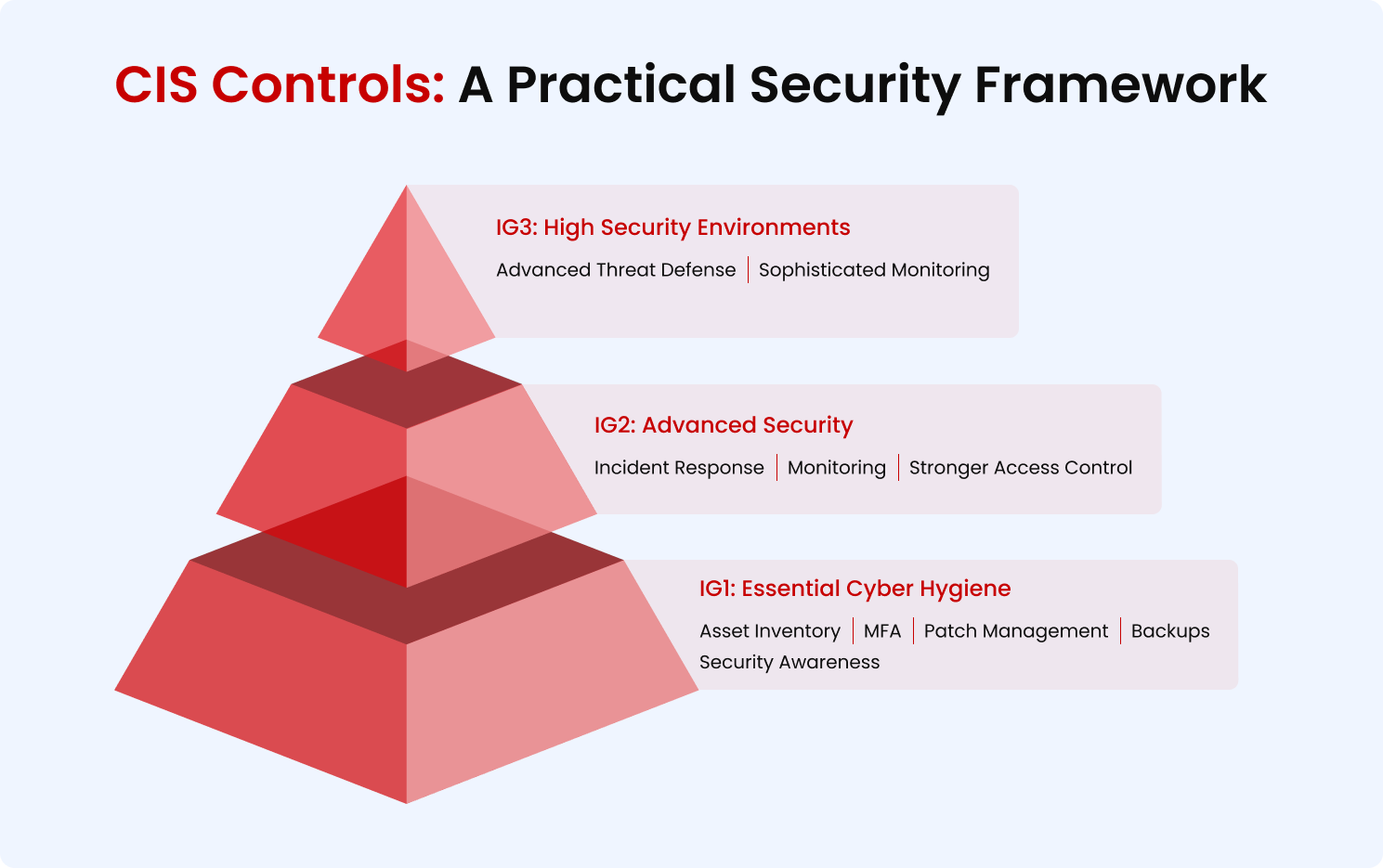
CIS Implementation Group 1 is what CIS calls “Essential Cyber Hygiene”. According to CIS, this is the set of Safeguards that all organizations should implement regardless of their size and budget. It covers more than 80% of the top attack techniques used by the most common threats such as ransomware, system intrusion attacks, etc.
CIS IG1 is the answer to the question, “Where should we start with security?”. CIS Controls and Safeguards are mapped to NIST 800-53, SOC 2 and ISO 27001. So, even if the end-goal is certification or compliance based on these, an organization can start with IG1 and get part of the way there while laying out a solid foundation. It is important to note that IG1 is still 15 Controls and 56 Safeguards, and there is an array of implementation approaches that can differ significantly in cost, complexity, and effectiveness. However, compared to NIST 80053 Rev 5 low baseline that includes roughly 149–150 required controls (base + selected enhancements), spanning governance, technical, and procedural requirements, CIS IG1 is materially smaller and more prescriptive.
Folding Zero Trust into Everything from Essentials to Advanced
Zero Trust can sit “underneath” CIS Controls across all three Implementation Groups and act as a unifying design principle that lets SMEs get more security out of every control they implement.
Folding Zero Trust into CIS Controls
Zero Trust is often described as “never trust, always verify, and enforce least privilege,” but in practice it is a way of designing identity, access, and network decisions so that you assume the network is already compromised. When you apply those ideas while implementing CIS Controls across IG1 to IG3, you avoid building a fragile, perimeter-centric environment that you later have to rearchitect.
For example, many IG1aligned safeguards, asset inventory, strong authentication, basic access control, secure configurations, and logging, can be implemented in a way that already follows Zero Trust principles: every user and device is identified, every access request is checked, and high value assets are segmented rather than exposed on a flat network. As you move into IG2 and IG3 with more advanced monitoring, network controls, and incident response, you can deepen the same pattern instead of layering new products on top of an old trust model.
This “Zero Trust by design” approach matters for SMEs because it lets you do more with less. Rather than buying one tool for VPN, another for identity, another for segmentation, and then trying to stitch them together later, you deliberately choose controls and configurations that give you multiple Zero Trust properties at once: central identity, least privilege access, micro-segmentation, continuous monitoring. CIS itself notes that Controls v8 can be used to prioritize a Zero Trust journey; aligning your CIS roadmap with Zero Trust concepts from the beginning reduces duplication, simplifies your environment, and makes each additional safeguard incrementally easier to operate.
Ingenuity: Getting More Done with Less
Creating a security architecture and an implementation approach that incorporates Zero Trust from foundational, essential hygiene-based security to advanced security that meets the requirements of leading security frameworks and goes beyond that to achieve advanced zero trust-based security requires ingenuity. Otherwise, it is easy to get lost in the multiplicity of security requirements and implement them in unwieldy, clunky, ineffective, and costly ways. SMEs lacking internal security expertise should work with security partners who can help them create future-proof security architectures and avoid such pitfalls.


.svg)



.png)

.png)
