How Regulation E Is Forcing Financial Institutions to Rethink Social Engineering Defenses
A customer logs into their banking app. They pass multi-factor authentication, enter the one-time password, and confirm a transfer. From the system’s perspective, everything looks legitimate. From a compliance perspective, everything looks documented. But from the customer’s perspective, they were just scammed.
- Feb 23, 2026

A customer logs into their banking app. They pass multi-factor authentication, enter the one-time password, and confirm a transfer. From the system’s perspective, everything looks legitimate. From a compliance perspective, everything looks documented. But from the customer’s perspective, they were just scammed.
Social engineering attacks have evolved. Instead of stealing credentials quietly, attackers now manipulate real users into moving their own money. The customer authorizes the transaction themselves, but under deception.
This is where Regulation E comes in. The regulation requires financial institutions to investigate and resolve unauthorized electronic fund transfers, which are defined as transfers initiated without the consumer’s actual authority. Traditionally, that meant clear-cut cases: stolen debit cards, hacked accounts, fraudulent ACH withdrawals. If the customer didn’t authorize it, the bank would reimburse it.
But what happens when the customer did authorize it, but not knowingly?
Think of authentication like a house key. Passing multi-factor authentication is like unlocking two locks. But social engineering is like someone convincing you to unlock your door because they’re pretending to be a firefighter. You used your key. You opened the door. But were you truly acting with informed intent?
Regulation E doesn’t tell companies how to prevent scams. Instead, it assigns liability and establishes expectations. And once liability enters the picture, security isn’t just technical; it’s regulatory. Passing MFA no longer proves true authorization. Logs record success, not manipulation.
Social engineering has shifted from being a fraud-loss problem to a regulatory exposure problem. Financial institutions now face a deeper question: How do you prove that a transaction was truly authorized when the customer was manipulated into pressing “send”? Understanding that question is central to modern finance defense.
Clear regulatory workflow
.png)
Social Engineering Doesn’t Break the System: It Uses It
The defining characteristic of social engineering is this: it doesn’t require a breach. The attacker doesn’t need to bypass MFA. They don’t need to exploit a vulnerability. They convince the customer to act.
That customer may believe they are protecting their funds, helping law enforcement, responding to their bank, or investing in something legitimate. From a user-interface perspective, everything looks normal. From a system perspective, everything logs correctly.
But from a consumer protection standpoint, something is wrong. Increasingly, regulators are asking whether institutions had reasonable safeguards in place to detect that something was off, even when credentials were valid.
That’s where the interpretation of Regulation E becomes more demanding. Authentication alone no longer closes the case.
The Real Question Regulators Are Asking
When a socially engineered payment occurs, the easy answer is to say: the customer authorized it. But the harder question is: did the institution do enough to detect deception? This is where many organizations are uncomfortable.
Because Regulation E is not a cybersecurity framework, it does not specify logging standards, behavioral analytics thresholds, or transaction monitoring rules. It is a liability framework.
And liability frameworks don’t ask whether you followed a full procedure perfectly. They ask whether you exercised reasonable security measures and consumer protection safeguards. That distinction matters.
In discussions we’ve had with financial institutions, a common pattern emerges. Fraud teams evaluate transaction legitimacy. Cyber teams monitor infrastructure integrity. Compliance teams ensure timelines are met.
But Regulation E exposure now lives in the space between those teams. That gap is where scrutiny builds.
Social Engineering Is Not a Customer Error. It’s an Incident
One of the most important mindset shifts institutions can make is simple: stop treating social engineering as a customer mistake.
When ransomware hits, no one shrugs and says, “Well, someone clicked a link.” There is a full incident response cycle. Logs are reviewed. Timelines are built. Signals are correlated. Documentation is preserved. Social engineering events deserve that same rigor.
If a customer was manipulated into moving funds, the institution should be able to demonstrate:
- What behavioral signals were present
- Whether risk scoring changed during the session
- Whether additional friction was considered or triggered
- How the investigation reached its conclusion
This is not about blaming the institution. It is about demonstrating structured protection and defensibility.
Ebryx helps organizations operationalize during this shift. We treat induced authorized fraud as a formal incident class. We look at fraud telemetry and cybersecurity signals together. We assess how investigation workflows are structured. And we evaluate whether the outcome is defensible, not just procedurally complete. Because under Regulation E, defensibility is everything.
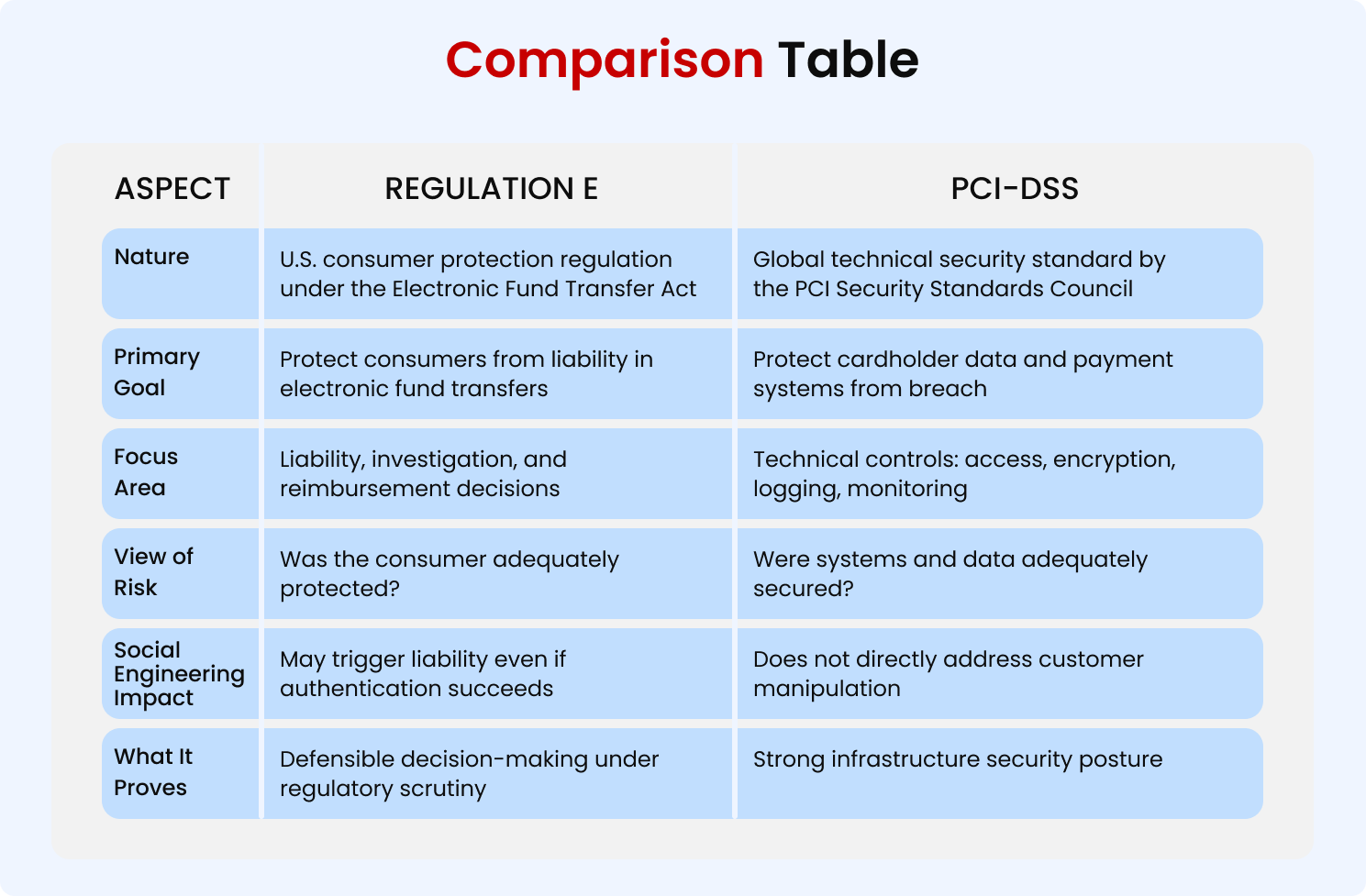
PCI-DSS: A Strong Foundation but Not the Finish Line
Most financial institutions already align with PCI-DSS. PCI-DSS is rigorous. It enforces access control, logging, encryption, segmentation, and incident response discipline. It protects the infrastructure. And that protection is critical.
If an attacker attempts to break into your systems, PCI controls matter immensely. They reduce breach risk and create forensic clarity. They are foundational to modern cybersecurity posture.
But here’s the reality we see across assessments: PCI compliance does not automatically translate into Regulation E defensibility, especially for social engineering cases.
PCI is designed to protect systems and data. Regulation E, especially in the context of social engineering, increasingly focuses on protecting customer intent and demonstrating reasonable safeguards.
If a scammer manipulates a customer into authorizing a transfer, your PCI environment may be perfectly secure. No intrusion. No malware. No exploited vulnerability. And still, you may face reimbursement exposure.
That’s why we often frame it this way: PCI gets you most of the way there, but not all the way. The remaining gap is behavioral and contextual, not purely technical.
It’s about anomaly detection focused on human patterns, not just system anomalies. It’s about contextual transaction controls. It’s about investigation documentation that aligns technical signals with regulatory expectations. That last layer is where many institutions are thin.
Getting from “Compliant” to “Defensible”
There’s a difference between being compliant and being defensible. Compliance means you can point to controls. Defensibility means you can explain decisions. Under Regulation E scrutiny, that difference becomes critical.
To move from compliant to defensible, institutions need tighter integration across fraud, cybersecurity, and governance functions.
- Fraud monitoring systems should not operate in isolation from security telemetry
- Behavioral analytics should inform transaction friction dynamically
- Investigation outcomes should be documented to clearly demonstrate reasonable consumer safeguards
Ebryx focuses on this integration. We assess how social engineering cases are detected, escalated, and reviewed. We identify where PCI-aligned controls stop short of behavioral oversight. We help institutions formalize social engineering as part of their incident response architecture, not just their dispute process.
This isn’t about adding complexity. It’s about connecting existing tools and workflows. Often, the tools are there; the integration is not.
The Shift Financial Institutions Can’t Ignore
Regulation E hasn’t dramatically changed on paper. But expectations around consumer protection in social engineering scenarios are evolving.
Institutions that rely solely on authentication success and post-transaction review may find that insufficient. Institutions that treat socially engineered payments as structured, telemetry-backed incidents will be better positioned.
Social engineering is not slowing down. Scam sophistication is increasing. Customers are being targeted with psychological precision. In that environment, infrastructure security remains essential. PCI-DSS remains foundational. Fraud detection remains critical.
But the differentiator going forward will be how well those layers work together and whether they collectively demonstrate reasonable consumer protection and regulatory defensibility.
Where Ebryx’s GRC and Security Fits In
Under Regulation E, investigations must be timely, documented, and defensible. Ebryx supports institutions in building structured investigation workflows that integrate:
- Fraud telemetry
- Device and behavioral intelligence
- Claim adjudication frameworks
- Regulatory reporting readiness
This ensures that when a social engineering claim arises, institutions are executing a repeatable, governance-backed process, not reacting ad hoc.
Embedding Compliance into Security Architecture
Rather than treating compliance as a post-incident requirement, Ebryx helps financial institutions embed regulatory considerations directly into security design:
- Risk-led control selection
- Policy development aligned with consumer protection standards
- Internal audit preparation
- Gap assessments against evolving regulatory expectations
The goal is simple: make compliance a built-in feature of the security ecosystem, not an afterthought.
Digital transaction flowing through layered shields
Conclusion
Social engineering has changed the rules of the game for financial institutions. Transactions that appear fully authorized may still carry hidden risks, and traditional security measures alone are no longer enough.
Regulation E, far from being a hurdle, provides a clear framework for accountability and consumer protection. It pushes institutions to rethink defenses, design smarter fraud controls, and document processes that can withstand regulatory scrutiny.
By following Regulation E as a guide rather than a constraint, finance companies can turn compliance into a strategic advantage, building systems that protect both users and their own reputation in a world where social engineering continues to evolve.


.svg)



.png)

.png)
