Privilege Escalation Explained. Lateral Movement in Action and How to Stop It
Imagine your organization’s security perimeter as a fortress. You’ve got thick walls, guarded gates, and surveillance cameras. But what if an attacker didn’t bother with the main entrance?
- Apr 06, 2026

Imagine your organization’s security perimeter as a fortress. You’ve got thick walls, guarded gates, and surveillance cameras. But what if an attacker didn’t bother with the main entrance? Instead, they found an unattended service account, a forgotten credential in a script, or an intern’s workstation left unlocked. That single point of entry could give them the keys to move anywhere inside your network. This is the reality of privilege escalation and lateral movement, two phases of a cyberattack that transform a minor breach into a full-scale compromise. The danger isn’t just that someone gets in; it’s that once inside, they can gain higher-level access and spread across systems at speed, all while staying under the radar.
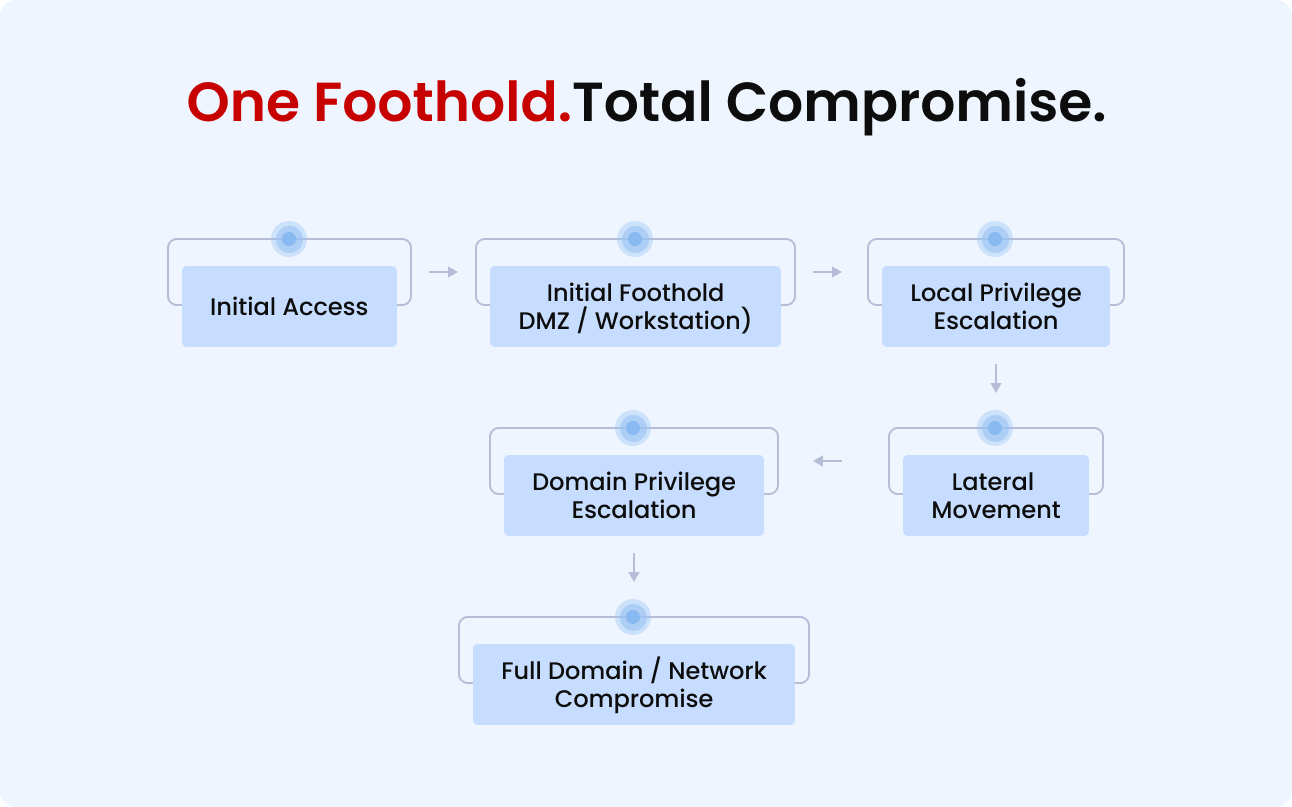
For boardroom, this isn’t a purely technical concern. It’s a business risk multiplier. Downtime, lost intellectual property, compliance violations, reputational fallout, these are the aftershocks of an attacker moving freely within your environment. According to IBM’s Cost of a Data Breach Report 2024, the average global cost of a data breach is now USD 4.88 million, marking a sharp 10% increase over just one year. Breaches involving stolen or compromised credentials had particularly long detection and containment times averaging 292 days making them among the costliest. The core message is simple: One foothold can equal total compromise. And unless your security strategy tests for and addresses these escalation paths, you may already have a breach waiting to happen.
Understanding Privilege Escalation
What Is Privilege Escalation?
At its core, privilege escalation is the act of obtaining permissions or access rights that a user (or process) was never intended to have. It’s not always about breaking into a system from the outside, it’s often about climbing the internal ladder of trust once you’re already in.
There are two main types:
Vertical Privilege Escalation
Moving from a lower level of access to a higher one. For example, a standard employee account gaining administrator or root privileges.
Horizontal Privilege Escalation
Gaining access to resources or accounts at the same level but belonging to other users, such as one employee accessing another’s private files.
Both forms allow attackers to bypass restrictions, disable security controls, and access sensitive systems. Once privileges are elevated, the attacker can make changes that grant them persistence, hide their presence, and facilitate further movement across the network.
Why It Matters to Your Business
Privilege escalation isn’t just a “tech problem.” For leadership, it’s an accelerator of impact. A phishing email that compromises one account may seem contained, but if that account has or can obtain administrative powers, the breach can spread to:
- Core business applications
- Confidential client data
- Intellectual property repositories
- Security and monitoring tools (ironically, to turn them off)
In short, the speed and scope of the attack expand dramatically once privilege escalation comes into play.
Importance of Security in DevOps
The importance of integrating security principles into DevOps practices stems from the growing sophistication of cyber threats. Traditionally, security has been the realm of specialists who operate independently. This siloed approach has become inadequate, and sometimes even detrimental, in the face of contemporary challenges. By adopting DevSecOps, organizations stand to gain not only in terms of rapid deployment and innovation but also by fortifying their defenses against potential breaches.
How Attackers Escalate Privileges
Once inside, attackers hunt for opportunities to amplify their control. This often involves exploiting weaknesses specific to the operating environment.
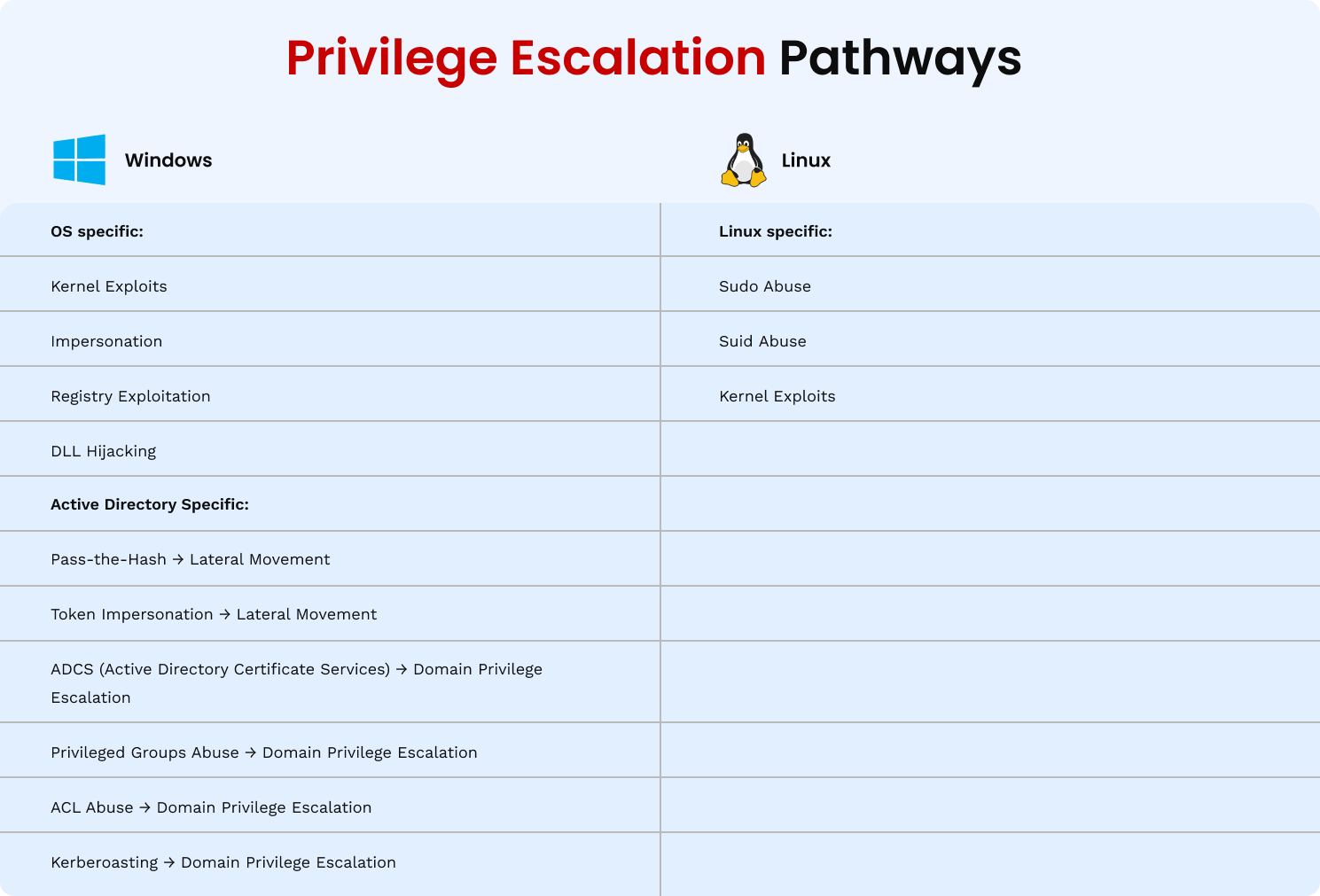
In Windows Environments
- Misconfigured Group Policy Objects (GPOs) – Weak permissions on GPOs allow attackers to inject malicious policies that execute code across multiple systems.
- Pass-the-Hash / Pass-the-Ticket Attacks – Instead of cracking passwords, attackers use stolen hashed credentials or Kerberos tickets to authenticate as legitimate users.
- Token Impersonation – Leveraging Windows access tokens to “become” another user, often one with higher privileges.
- Misconfigured Services (Writable BinPath): If the service’s executable path is writable, attackers can swap it with malicious code and restart the service to gain SYSTEM access.
- Modifiable Scheduled Tasks: Weakly secured tasks running as SYSTEM can be edited by lower-privilege users, letting attackers insert malicious commands and escalate privileges.
In Linux Environments
- ‘sudo’ Misconfigurations – Granting unnecessary ‘NOPASSWD’ privileges or allowing wildcard paths that can execute unintended commands.
- SUID/SGID Binary Exploitation – Executing binaries with elevated privileges due to insecure file permissions.
- Credential Exposure – Plaintext passwords or keys stored in environment variables, shell history, or configuration files.
- Kernel Exploits – Taking advantage of unpatched kernel vulnerabilities to jump straight to root access.
Why These Techniques Work
The success of privilege escalation often comes down to misconfigurations, credential mishandling, and delayed patching, all common in busy IT environments. Attackers exploit the fact that many organizations focus heavily on perimeter defenses but don’t always test the “inside game” as thoroughly.
Credential Harvesting
Before attackers can climb the privilege ladder, they need the keys, and those keys are credentials. Credential harvesting is the process of stealing usernames, passwords, tokens, and keys that grant access to systems, services, and applications.
Attackers use a variety of methods to collect them:
Dumping Passwords from Memory
- Tools like Secretsdump and Mimikatz extract credentials from the Windows LSASS process memory.
- On Linux, attackers target /etc/shadow to retrieve hashed passwords for offline cracking.
Harvesting Browser-Stored Passwords
- Many browsers save credentials in local files, often in poorly protected formats.
- If a user logs into corporate services from their browser, those credentials could be stolen in seconds.
Scraping Credentials from Scripts and Config Files
- Developers sometimes leave API keys, SSH credentials, or database logins hardcoded in scripts or stored in version control.
- These become easy pickings once an attacker gains local access.
Memory Scraping from Running Applications
- Attackers can scan memory for plaintext secrets, particularly in applications that don’t properly clear sensitive data after use.
Why this matters to leadership: Credential harvesting is fast, automated, and opportunistic. Once an attacker has one set of credentials, they often find others in quick succession, multiplying their potential impact before anyone even notices they’re there.
Lateral Movement in Action
Privilege escalation isn’t the endgame; it’s the launchpad. Once an attacker has higher privileges, they can move laterally across your network, targeting more valuable systems and data.
How Attackers Pivot
- SSH Tunneling: Attackers create secure tunnels through compromised hosts to forward traffic, effectively turning them into steppingstones for further compromise.
- Reverse Proxies: By setting up a reverse proxy, attackers can redirect traffic through an infected machine, masking their true origin and evading perimeter defenses.
- Protocol Tunneling (DNS/ICMP/HTTP): Advanced attackers encapsulate malicious traffic inside legitimate protocols like DNS, ICMP, or HTTP to sneak past firewalls and intrusion detection systems.
- Remote Service Creation – Installing and running malicious services on other machines.
- Windows Management Instrumentation (WMI) – Remotely executing commands on other endpoints.
- RDP Hopping – Using Remote Desktop Protocol to move from one compromised system to another.
- SSH Key Abuse – Leveraging stolen private keys to access Linux servers without needing passwords.
What It Looks Like in Network Logs
Security teams who know where to look can often spot lateral movement by watching for patterns such as:
- Unusual login times (e.g., admin logins at 3 a.m.)
- A single workstation logging into multiple servers in quick succession
- Credential use from IP addresses or locations not tied to the account’s normal activity
- High volumes of inter-server traffic that don’t match regular workflows
For leaders, this is where the “domino effect” becomes visible: a single compromised point can turn into dozens of compromised endpoints within hours.
Real-World Example: WannaCry & EternalBlue
A stark illustration of lateral movement at scale is the 2017 WannaCry ransomware outbreak. It began exploiting a Windows SMB vulnerability known as EternalBlue (originally a U.S. NSA-developed exploit leaked by the Shadow Brokers group).
- Initial foothold: The worm exploited vulnerable SMBv1 services on Windows machines connected to the internet.
- Privilege escalation: Once inside a host, it used local privileges to deploy ransomware payloads and disable recovery options.
- Lateral movement: Eternal Blue allowed WannaCry to propagate autonomously across the network, infecting other vulnerable machines without further human action.
- Impact: Over 200,000 computers across 150 countries were affected, crippling organizations from the UK’s National Health Service (NHS) to FedEx.
Source: Microsoft Security Response Center – WannaCry Guidance
The WannaCry incident demonstrated just how quickly an exploit chain can spiral. One unpatched system led to global operational disruption, costing billions in losses.
For leadership, the lesson is clear: attackers don’t stop at the door, they roam the halls. And in a connected environment, movement from one compromised machine to critical infrastructure is a matter of minutes, not days.
How VAPT Discovers the Hidden Attack Chain
Many organizations run vulnerability scans and believe they’ve covered their bases. But traditional scanning is like checking individual bricks for cracks while ignoring how those cracks connect into a fault line.
Vulnerability Assessment and Penetration Testing (VAPT) goes beyond isolated weaknesses, it mimics the mindset of an attacker, chaining multiple small flaws into a path that can lead to a catastrophic compromise.
Ebryx’s Vulnerability Assessment and Penetration Testing (VAPT) is designed to give leadership a clear picture of how those connections could impact the business if left unchecked. Instead of drowning you in raw data, the outcome is a strategic view of your risk: where privilege escalation could occur, where movement across systems is possible, and where business-critical assets could be at stake.
The result? You gain the clarity to prioritize fixes that actually shut down the most dangerous pathways, the ones that could turn a minor incident into a complete compromise.

Beyond Vulnerability Scans
- Static vulnerability scanners produce lists of known issues but don’t explore how those issues can be combined.
- VAPT actively tests these combinations, revealing the “attack path,” the step-by-step route an adversary could take from initial foothold to domain-wide control.
Attack Path Analysis in Action
Consider a VAPT engagement that uncovers:
- A service account vulnerable to Kerberoasting (cracking weak Kerberos tickets).
- Use of that account’s credentials to escalate privileges via a User Account Control (UAC) bypass.
- Active Directory Certificate Services (ADCS) was identified as misconfigured, allowing the abuse of certificate templates to escalate privileges and request certificates for higher-privileged accounts.
- Misconfigured privileged accounts & ACL abuse can lead to targeted chained attacks leading to lateral movement or domain admin compromise.
- Lateral movement to a domain controller using stolen NTLM hashes.
- Dumping of the LSASS process to retrieve domain admin credentials.
Individually, each of these findings might be logged as “medium severity.” But together, they form a critical chain capable of complete network takeover, exactly the scenario real attackers aim for.
Executive Takeaways: Why Leadership Should Care
- One compromised point can be enough to cascade into organization-wide access if escalation paths are left open.
- Attackers think in chains, not checklists and risks must be addressed the same way.
- Ebryx VAPT gives you a clear picture of the pathways most likely to be exploited, helping you focus on what matters most.
- The cost of prevention is always less than the cost of recovery, both in dollars and in brand trust.
- Effective security requires leadership attention. When executives understand the escalation and movement risk, they can ensure the right resources and urgency are applied.
Conclusion
Modern cyberattacks rarely succeed through one big, obvious vulnerability. They succeed by chaining together smaller, overlooked ones until they reach the crown jewels of your business.
The bad news? Those chains often already exist.
The good news? Ebryx can help you see and break them before anyone else does.
That’s why Ebryx’s approach goes beyond finding weaknesses in isolation. We simulate how those weaknesses interact, the chain reaction an attacker would trigger, so leadership can see the true scale of risk.
Don’t let the first domino fall. See the risk. Stop the chain. Stay secure.


.svg)



.png)

.png)
