How CIS IG2 Builds Upon IG1 to Strengthen Cyber Hygiene
Essential Cyber Hygiene (ECH) is no longer “nice to have,” it’s a baseline requirement. Organizations that only implement fundamental controls are often vulnerable to advanced threats, internal misconfigurations,
- Apr 14, 2026

Essential Cyber Hygiene (ECH) is no longer “nice to have,” it’s a baseline requirement. Organizations that only implement fundamental controls are often vulnerable to advanced threats, internal misconfigurations, and evolving attack techniques. The Center for Internet Security (CIS) provides a framework of prioritized, implementable, and prescriptive security controls to help organizations reduce their exposure to common cyber threats.
These controls are divided into three Implementation Groups (IGs) - IG1, IG2, and IG3, which serve as a roadmap for organizations to incrementally build their security maturity. While IG1 focuses on foundational security practices, IG2 builds upon these essentials to address more dynamic risks and operational complexity. For technology leaders, CISOs, engineering managers, and DevSecOps leads, understanding how IG2 strengthens and extends IG1 is critical for making strategic, risk-based decisions.
This blog post will guide you through the key differences between IG1 and IG2, breaking down how IG2 builds on IG1 to enhance your organization’s Essential Cyber Hygiene, control by control. Whether you're preparing for compliance, seeking to scale securely, or simply looking to mature your security program, this is your practical roadmap.
What Is IG1? The Foundation of Essential Cyber Hygiene
Who needs IG1?
IG1 is designed with smaller organizations and those with limited cybersecurity expertise or budget in mind. It offers a foundational set of 56 safeguards that cover the most basic and essential steps any organization should take to prevent common cyberattacks. Think of IG1 as a cybersecurity checklist for small IT teams or solo admins trying to keep the lights on while maintaining some level of protection. It's about creating a minimal viable defense that stops opportunistic attacks.
Basic ECH achieved via 56 safeguards
The 56 safeguards in IG1 are aligned to cover key areas like asset inventory, software management, vulnerability remediation, and basic access control. These safeguards emphasize visibility, control over systems and data, and basic perimeter defense. While they may not protect against highly targeted threats, they cover a significant percentage of the attack surface exploited by commodity threats, phishing, and malware.
Limitations of IG1 in complex environments
As useful as IG1 is, it doesn't scale well for organizations with distributed networks, remote workforces, cloud-native apps, or complex data flows. The static nature of IG1 controls lacks adaptability for threat intelligence, proactive monitoring, or granular configuration management. In such environments, adversaries can easily bypass basic protections. This is where IG2 enters as a much-needed evolution, extending protections from a reactive to a proactive stance.
Introducing IG2
Why IG2 exists
With 80% of organizations operating in multi-cloud environments, IG2 becomes essential for extending ECH to these complex architectures. IG2 was created to meet the needs of organizations facing more sophisticated cyber threats or operating in environments that require tighter controls, like healthcare, finance, or tech enterprises. These organizations often have diverse infrastructure (on-prem, cloud, mobile), handle sensitive customer or internal data, and operate across multiple departments. IG2 recognizes that simply knowing what assets you have isn't enough; you must monitor, validate, and actively manage them.
IG2 audience
Organizations that benefit most from IG2 typically have dedicated IT and security teams, a mix of on-prem and cloud infrastructure, and compliance requirements such as HIPAA, PCI-DSS, or SOC 2. They're not yet at the threat level of critical infrastructure (IG3), but they need more than basic defenses. If your company supports remote employees, manages sensitive data, or integrates third-party services, IG2 is the natural next step.
IG2’s 74 additional safeguards: The expansion strategy
IG2 includes all the controls from IG1 but layers on 74 additional safeguards, bringing the total to 130. These added safeguards deepen protections around identity, data, software, configuration, and threat detection. IG2’s expansion isn’t just about volume; it’s about increasing depth and precision. The goal is to reduce cyber risk by shifting from ad hoc processes to systematic, monitored, and enforced security practices.
IG1 vs. IG2 in Strengthening Cyber Hygiene

From “reactive” hygiene to “proactive” security
IG1 enables organizations to handle cybersecurity reactively responding to known threats with basic tools. IG2 transforms that posture by embedding proactive strategies: asset validation, regular audits, and automated detection. Rather than waiting for alerts after a compromise, IG2 organizations seek early warning signs and implement defenses that preempt attacks. This transition from reactive to proactive is what defines robust cyber hygiene.
IG2 enables context-aware defenses (asset, identity, and data-based)
While IG1 treats security controls in silos, IG2 promotes contextual security understanding who’s accessing what, from where, and why. With identity-based access controls, data classification, and more precise asset management, IG2 safeguards allow for real-time, risk-aware responses. This evolution allows security teams to tailor responses to specific threats and user behaviors rather than using a one-size-fits-all model.
More automation, formalization, and validation required
IG2 demands higher maturity in operations. Controls require not just implementation, but evidence; logs, policies, automation, validation tools. For example, while IG1 may involve manual asset discovery, IG2 encourages the use of automated scanning and continuous monitoring to validate asset integrity. This level of rigor increases accountability and ensures that hygiene isn’t just performed, it’s sustained and auditable.
IG2 Builds Monitoring and Validation on IG1 Inventory

IG1 Focus: Asset discovery
At the IG1 level, asset discovery is primarily a manual or semi-automated task focused on knowing what hardware exists in the organization. The objective is to ensure that all enterprise assets servers, laptops, networking devices, are documented and tracked. This foundational step helps organizations establish visibility over their environment, reducing the chance of unmonitored endpoints becoming security blind spots.
IG2 Enhancements: Inventory validation, unauthorized asset detection
IG2 takes this further by adding automation and validation. It’s not enough to know what assets you have; you need to constantly verify that those assets are still authorized, up-to-date, and properly configured. IG2 introduces safeguards like continuous asset scanning, integration with CMDBs, and automatic flagging of rogue or unknown devices on the network. These capabilities are vital in dynamic environments like cloud, DevOps, or remote-first workplaces where assets are frequently spun up and down.
Ensure only known and secure assets operate in the network
By validating and monitoring assets continuously, IG2 ensures that your security posture is not static, but responsive. This reduces dwell time for adversaries, limits the chance of shadow IT, and ensures that every system operating within the environment is accounted for, authorized, and hardened dramatically enhancing essential cyber hygiene.
Software Management
IG1
Installed apps list
Manual updates
Reactive patching
IG2
IG1: List what’s installed
In IG1, software management focuses on maintaining a complete inventory of all applications installed across enterprise systems. This includes identifying software versions, publishers, and known vulnerabilities. The main goal is awareness, so that IT teams know which software exists and can begin managing potential risks, particularly from outdated or unauthorized applications.
IG2: Detect unauthorized or vulnerable software using tools
IG2 builds on this foundation by integrating software monitoring tools that can automatically detect when unauthorized or vulnerable software is installed. This includes capabilities like real-time scanning, version validation against vulnerability databases (e.g., NVD or CVE feeds), and alerting when unapproved applications appear. These tools help organizations maintain software hygiene continuously, not just periodically.
Reduce software attack surface through automation
By moving from static inventories to real-time detection and enforcement, IG2 significantly reduces the attack surface. Unpatched software is one of the most exploited attack vectors; with automated discovery and response, organizations can act fast, deprecating or updating at-risk applications before they're weaponized. This proactive control dramatically strengthens ECH across dynamic environments.
IG2 Adds Classification and Encryption
IG1: Basic data access control
Under IG1, data protection is approached through basic access controls ensuring that only authorized users can access sensitive information. This typically includes user account permissions and access lists for shared folders or systems. However, it often lacks nuance around data types, sensitivity levels, or usage context.
IG2: Role-based access + encryption in transit and at rest
IG2 introduces data classification, the process of tagging data based on sensitivity (e.g., confidential, internal, public) and matching access controls accordingly. It also requires encryption of data both in transit and at rest, ensuring protection even if data is intercepted or storage media is compromised. These are no longer “nice to have” features but are essential safeguards that IG2 mandates for organizations handling proprietary or regulated data.
Minimize data leaks, even if a breach occurs
With IG2’s added layers of encryption and classification, the organization reduces the blast radius of a data breach. Even if attackers bypass perimeter defenses or internal controls, access to meaningful data is still restricted. Data becomes harder to exploit or monetize, and incident response becomes more surgical and confident. This elevates data hygiene from simply limiting access to actively protecting confidentiality and integrity.
Secure Configuration
IG1: Ensure default settings are changed
At the IG1 level, secure configuration focuses on modifying out-of-the-box settings that are often insecure. This includes changing default passwords, disabling unnecessary ports and services, and applying basic security hardening to operating systems and applications. These actions are crucial first steps in reducing the “low-hanging fruit” that attackers often exploit.
IG2: Enforce baseline configurations + change management
IG2 goes far beyond the basics. It requires organizations to define, document, and enforce baseline configuration standards across all system types workstations, servers, cloud instances, network devices. It also introduces change control mechanisms, ensuring that any deviation from the baseline is tracked, justified, and approved. Tools like configuration management platforms (e.g., Ansible, Chef, or Group Policy Objects) play a key role in implementing and monitoring these baselines.
Resilience against misconfiguration and human error
Misconfiguration is one of the most common causes of security incidents. By establishing baselines and governing changes, IG2 turns configuration management into a controlled, auditable, and proactive process. This greatly reduces the risk of accidental exposure or configuration drift leading to a more stable and secure infrastructure overall and significantly reinforcing cyber hygiene.
IG2 Brings Role-Based Governance
IG1: Limit admin privileges
In IG1, the principle of least privilege is applied at a basic level. Admin rights are restricted to those who truly need them, and efforts are made to ensure that regular users do not have elevated access by default. This helps contain potential damage if a user account is compromised.
IG2: Role-based access, periodic access review, MFA enforcement
IG2 introduces role-based access control (RBAC) frameworks, ensuring access is systematically aligned with job duties. It also requires periodic reviews of user permissions to catch privilege creep, where employees have the access, they no longer need. Additionally, IG2 enforces Multi-Factor Authentication (MFA) for all administrative access, and ideally for all users, especially when accessing cloud services.
Minimize privilege abuse and account compromise
By introducing governance and continuous oversight over identity and access, IG2 helps minimize insider threats, privilege escalation, and the fallout from compromised accounts. Combined with MFA, these measures create a layered identity perimeter that is far more difficult for attackers to penetrate, further strengthening essential cyber hygiene across the organization.
Vulnerability Management
IG1: Monthly scanning and patching
IG1 promotes a regular schedule typically monthly for scanning systems and applying critical patches. This frequency is sufficient for small environments where change is infrequent and risk is relatively low. However, it often lacks context or prioritization, treating all vulnerabilities with similar urgency.
IG2: Contextual risk assessment and prioritization
IG2 elevates vulnerability management by integrating context-aware prioritization. Instead of patching everything on a schedule, organizations assess vulnerabilities based on factors such as asset criticality, exposure level, exploitability, and business impact. This often involves using vulnerability management platforms that incorporate CVSS scores and real-world threat intelligence.
Focus on threats most likely to affect your environment
By focusing resources on the vulnerabilities that pose the greatest real-world risk, IG2 enables a much more efficient and impactful security posture. This strategy reduces downtime, avoids patch fatigue, and ensures that mitigation efforts are aligned with the actual threat landscape key aspects of a mature cyber hygiene program.
IG2 Enables Threat Detection

IG1: Basic logging
Under IG1, logging is treated as a foundational visibility mechanism. Systems are expected to generate logs for significant events such as logins, configuration changes, and software installations. However, these logs are often stored locally or dispersed across systems, with little effort toward aggregation, correlation, or real-time analysis.
IG2: Centralized log aggregation and alerting
IG2 introduces centralized logging infrastructure, such as a Security Information and Event Management (SIEM) system, to aggregate, parse, and monitor logs across the enterprise. It also includes real-time alerting and automated responses to suspicious behaviors, such as multiple failed login attempts, unauthorized access to sensitive files, or anomalies in user behavior.
Early detection of anomalous behavior
With centralized logging and intelligent alerting, organizations can move from passive logging to active threat detection. IG2 empowers teams to detect and respond to threats before damage occurs, significantly strengthening essential cyber hygiene. It transforms logging from an afterthought into a critical, real-time security function.
Malware Defenses
IG1: Traditional antivirus
IG1-level defenses rely on traditional antivirus solutions to detect known threats using signature-based detection. While this protects against common malware strains, it is increasingly ineffective against polymorphic malware, fileless attacks, and targeted threats that evade traditional tools.
IG2: Application allowlisting, endpoint behavior analysis
IG2 enhances malware defense by requiring application control mechanisms like allowlisting or blocklisting, which only permit approved software to execute. Additionally, IG2 introduces endpoint detection and response (EDR) tools that monitor system behavior for signs of compromise, such as unexpected file changes or unusual process activity even in the absence of known signatures.
Prevent modern malware and ransomware
With proactive defenses that control what can run and detect abnormal behavior in real-time, IG2 closes the gaps left by traditional antivirus. This approach significantly reduces the risk of successful malware deployment and ransomware infections, reinforcing the organization's cyber hygiene posture with advanced, adaptive defenses.
Recovery and Resilience

IG1: Maintain regular backups
In IG1, the emphasis is on maintaining routine backups of critical data and systems. These backups are often manual or semi-automated and may be stored on the same network as production systems, making them vulnerable to encryption or deletion by ransomware.
IG2: Test recovery processes, isolate backups
IG2 goes much further by requiring isolated, immutable, and encrypted backups. It also introduces formal disaster recovery testing procedures to verify that backups can actually be restored under real-world conditions. This includes establishing Recovery Time Objectives (RTOs) and Recovery Point Objectives (RPOs) aligned with business needs.
Ensure recovery from any incident, not just accidents
By emphasizing resilience and preparedness, IG2 ensures organizations can bounce back from not just operational failures, but full-scale cyber incidents. Testing, isolating, and securing backup systems elevates recovery from a reactive process to a strategic pillar of cyber hygiene, reducing downtime and reputational risk in the face of ransomware or destructive attacks.
IG2 Adds Precision Filtering
IG1: Basic web and email protections
IG1 includes straightforward protections like spam filters, URL blacklists, and basic antivirus scanning of email attachments. These defenses are helpful for blocking widespread phishing campaigns and known malicious sites, but often lack depth, precision, and the ability to catch more sophisticated social engineering or zero-day exploits.
IG2: Sandboxing, domain filtering, advanced user awareness
IG2 significantly upgrades web and email security by introducing sandboxing for attachments and links where content is opened in a safe environment to detect suspicious behavior before it reaches the user. It also includes domain-based filtering and DNS security to block access to malicious infrastructure. Coupled with targeted security awareness training for at-risk users (e.g., executives, finance staff), these controls offer multi-layered defenses.
Neutralize phishing and drive-by downloads
Based on Cisco reports, 94% of malware is delivered via email, underscoring the need for IG2’s advanced filtering and user awareness safeguards. With these precision tools in place, IG2 provides organizations with the ability to detect and block phishing attempts and malware-laced websites before they reach endpoints. This reduces user error, one of the most exploited vectors in cybersecurity incidents, and greatly enhances everyday cyber hygiene.
IG2 Enables DevSecOps
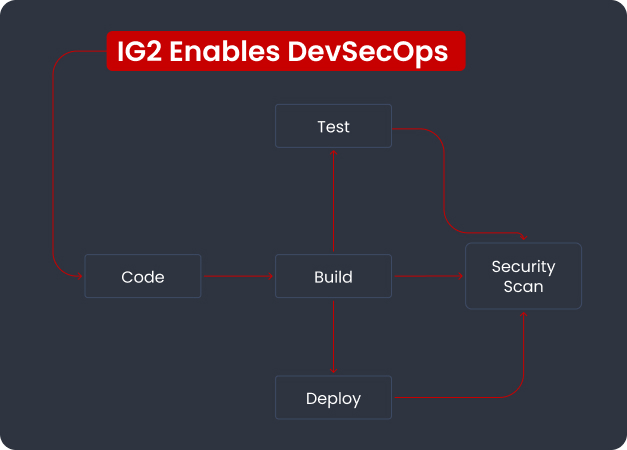
IG1: Update software regularly
At the IG1 level, software security is reactive and largely operational focused on keeping operating systems and applications up to date. It doesn’t usually extend into the development lifecycle, nor does it address custom applications or third-party libraries introduced through DevOps pipelines.
IG2: Threat modeling, secure coding practices, code review
IG2 integrates cybersecurity into the software development lifecycle (SDLC) by promoting practices like threat modeling, secure code training for developers, static and dynamic code analysis, and peer-reviewed code commits. These safeguards ensure that applications are built securely from the ground up, not patched reactively after deployment.
Reduce vulnerabilities in custom applications
As organizations increasingly rely on proprietary applications and cloud-native architectures, integrating security into development becomes essential. IG2 enables a DevSecOps model where security is embedded early, reducing the cost and risk of vulnerabilities and dramatically raising the bar for cyber hygiene at the application level.
Third-Party and Cloud Services
IG1: Choose secure vendors
IG1 encourages organizations to evaluate third-party providers before onboarding, often through checklists or contractual commitments. However, it lacks mechanisms for validating ongoing compliance or monitoring vendor risk post-engagement, especially in dynamic cloud environments.
IG2: Contractual SLAs, monitoring service provider compliance
IG2 introduces a more structured and accountable approach. It requires security clauses in vendor contracts, well-defined service level agreements (SLAs), and ongoing risk assessments. It also recommends organizations implement third-party risk monitoring tools and request evidence of provider compliance with frameworks like SOC 2, ISO 27001, or industry-specific regulations.
Shared responsibility in cloud and SaaS environments
With more data and services outsourced, IG2 ensures that cybersecurity doesn’t stop at the organizational boundary. By enforcing a shared responsibility model, organizations can better protect their cloud workloads, customer data, and business operations solidifying cyber hygiene across their extended digital ecosystem.
Incident and Penetration Readiness
IG1: Have an incident plan
At the IG1 level, organizations are expected to have a basic incident response plan that outlines roles, responsibilities, and initial steps to take during a cyber event. However, these plans are often static documents that may not be well-tested or integrated with technical response capabilities. The focus is more on preparedness than on practice.
IG2: Regular exercises, penetration testing, red teaming
IG2 takes incident response to a strategic level by introducing routine tabletop exercises, technical simulations, and full-scale red team engagements. Organizations are required to test their incident response processes under real-world conditions, identify gaps in detection and communication, and refine their plans accordingly. Penetration tests go beyond compliance; they simulate an attacker's behavior to uncover weaknesses in people, processes, and technologies.
Improve response time and reduce breach impact
This shift from planning to validated readiness makes a substantial difference in reducing breach impact. Organizations that practice responses in advance are quicker to detect, contain, and recover incidents. IG2 ensures that cyber hygiene includes operational resilience, not just preventative measures.
Transitioning from IG1 to IG2

Assessing your current maturity
The journey from IG1 to IG2 begins with a realistic maturity assessment. Organizations should identify which IG1 safeguards are already fully implemented, where there are gaps, and whether existing processes are scalable. This can be achieved through internal audits, gap analyses, or third-party assessments using tools like the CIS Controls Self-Assessment Tool (CSAT).
Building a roadmap for adopting IG2
With the assessment in hand, leaders should create a phased implementation roadmap that prioritizes high-impact IG2 safeguards. Areas like centralized logging, role-based access control, and vulnerability prioritization usually deliver strong early returns. The roadmap should also align with business objectives, available resources, and compliance needs.
Gaining stakeholder buy-in (Board, Engineering, Ops)
Successfully adopting IG2 requires alignment across departments from the boardroom to the server room. Senior leadership must understand the risk reduction and ROI associated with IG2, while engineering and operations teams need to see it as enabling secure scalability, not additional overhead. Clear communication of goals, risks, and benefits is critical for long-term success.
Conclusion
CIS IG2 is not a departure from IG1; it’s a strategic enhancement that shifts organizations from a posture of basic protection to one active risk management and resilience. By building on IG1’s foundational safeguards and introducing automation, validation, and deeper context, IG2 strengthens Essential Cyber Hygiene in ways that are both measurable and mission critical.
For senior technology leaders, CISOs, and DevSecOps managers, adopting IG2 is not just a matter of compliance; it’s a blueprint for sustainable security maturity. It ensures that your defenses scale as your organization grows, and that your cyber hygiene evolves to meet the complexity of today’s digital threats.
Now is the time to assess where you stand, define your next steps, and start building toward IG2 maturity. Your organization’s resilience and reputation depend on it.
FAQs
1. What is the main difference between IG1 and IG2?
IG1 focuses on essential cyber hygiene using basic safeguards, while IG2 expands on these by introducing more automation, monitoring, and proactive controls tailored for more complex environments.
2. Can an organization skip IG1 and go directly to IG2?
No. IG2 is built on top of IG1. An organization must fully implement IG1 safeguards before layering on IG2’s additional controls.
3. How long does it take to transition from IG1 to IG2?
It varies by organization size, existing maturity, and resource allocation. A phased implementation over 6–12 months is common for mid-sized enterprises.
4. Is IG2 required for compliance frameworks like SOC 2 or HIPAA?
While IG2 is not legally mandated, many of its safeguards align with requirements in SOC 2, HIPAA, and NIST fram1eworks. Adopting IG2 often accelerates compliance efforts.
5. What tools can help automate IG2 safeguards?
Tools like SIEM platforms, endpoint detection and response (EDR), vulnerability scanners, and configuration management systems are essential for automating IG2 control enforcement and monitoring.

.png)

.png)
